DeFi Custody Risks Explained: Who Really Holds Your Funds?
By Jorge Rodriguez — Risk Management
How the three custody layers in DeFi work and where risk lives in each
A pre-deposit checklist for evaluating smart contract custody before committing funds
The key difference between protecting your wallet and protecting your deposited funds
Introduction
Most DeFi participants spend hours comparing yield rates across protocols, searching for the best APY on stablecoin deposits or lending positions. Very few ask the question that matters most before that first deposit: who actually controls your funds at each step? **DeFi custody risks** operate across three distinct layers. The first is your wallet, where your private key determines ownership. The second is the protocol layer, where smart contract code takes custody of anything you deposit. The third is the infrastructure underneath, including upgrade authorities, admin keys, and governance mechanisms that can alter how the protocol behaves after you have already committed funds. Understanding how these layers interact is not a technical exercise reserved for developers. It is the foundational risk question every DeFi participant should answer before depositing. Custody failures account for some of the largest losses in DeFi history, and most of them had nothing to do with the victim's wallet being compromised. This guide maps the custody layers from wallet to protocol to smart contract, explains where real risk lives at each level, and gives you a practical framework for evaluating any protocol before you deposit. A dedicated section covers Solana-specific custody nuances, including program upgrade authorities and the multisig standards responsible protocol teams use to govern them. As a reference point throughout: Lince builds its yield products around a non-custodial model where users retain access to their private key throughout the deposit lifecycle. That design philosophy serves as a useful benchmark for what sound protocol custody architecture looks like in practice. For a broader view of how custody risk fits alongside other categories, see [DeFi Yield Risks Explained](/blog/risk-management/defi-yield-risks-explained).
What DeFi Custody Actually Means
**The Three Layers of DeFi Custody** **Custody** in DeFi refers to who has technical and practical control over your assets at any given moment. Unlike traditional finance, where a bank holds funds under regulatory supervision with deposit insurance backstops, DeFi custody is governed by code and cryptography rather than legal frameworks or institutional accountability. The wallet layer is where most people start their mental model. Your **private key** is the cryptographic proof of ownership for any assets held in a wallet address. If you control the private key, you control the assets. If someone else controls it, they can move your funds without your permission at any time. The protocol layer is where most mental models end prematurely. The moment you deposit funds into a lending protocol, a yield vault, or a liquidity pool, those funds leave your wallet. They are held by the smart contract code of that protocol. Your wallet holds a claim on those funds, but the contract controls them under its defined logic until you withdraw. The hybrid layer sits between those two and includes models like MPC wallets, account abstraction, and social recovery systems that distribute key control across multiple parties or mechanisms. These add recovery flexibility but introduce their own custody trade-offs and trust assumptions.  **Why DeFi Custody Risk Is Different** Traditional finance has safety nets. Bank deposits in many jurisdictions benefit from government-backed insurance, dispute mechanisms, and regulated recourse when something goes wrong. DeFi has none of these by default, and no regulatory body currently mandates equivalents. On-chain transactions are irreversible. If a smart contract exploit drains a protocol while your funds are deposited, no authority can reverse the transaction. No regulator intervenes. No chargebacks exist. This is why getting custody right at every layer, before depositing, is the only meaningful form of protection available to a DeFi user. Cross-chain context adds further complexity. Ethereum, Solana, and Base each have different smart contract models, upgrade mechanisms, and tooling for verifying custody risk. A framework that works for evaluating an Ethereum protocol needs adjustment before applying it to a Solana program, particularly around upgrade authority mechanics that are unique to the Solana account model. According to [DeFi Llama](https://defillama.com), total value locked across DeFi protocols regularly reaches into the hundreds of billions of dollars. At that scale, smart contract custody is one of the most consequential trust decisions in modern finance, and it is one where the burden of evaluation falls entirely on the individual depositor.
Custodial Wallets: What You Are Really Agreeing To
**How Custodial Arrangements Work** A **custodial wallet** is one where a third party holds your private key. Centralized exchanges, some brokerage platforms, and many beginner-friendly apps fall into this category. When you deposit funds into these platforms, you give up direct control. The platform holds the assets; you hold an IOU that depends entirely on that platform's continued solvency and willingness to honor withdrawals. Access controls are set entirely by the platform. They can freeze withdrawals, impose limits, require additional identity verification, or suspend your account based on their own policies, regulatory demands, or internal financial pressure. You have no technical ability to bypass these controls because you do not hold the key. **The Real Risks of Custodial Arrangements** Protocol insolvency is the most severe custodial risk. When a centralized custodian becomes insolvent, depositors typically become unsecured creditors in a bankruptcy proceeding. They may wait years to recover a fraction of their assets, or recover nothing at all. High-profile exchange collapses have demonstrated this dynamic clearly, and no regulatory framework has yet introduced the kind of per-account deposit protection that exists in traditional banking. Withdrawal freezes are a softer but more common manifestation of the same underlying problem. Platforms under liquidity stress have paused withdrawals unilaterally, leaving users locked out of their own funds for weeks or months. These freezes are typically permitted under the terms of service that custodial users agree to when signing up. Regulatory seizure adds a different vector entirely. Government authorities in various jurisdictions have compelled custodians to freeze specific accounts or transfer assets to enforcement agencies. Users of self-custody solutions are not immune to regulatory risk, but custodial users face a much more direct and immediate exposure to government-ordered access restrictions. Platform-side security breaches represent a fourth risk category. A custodian holding private keys for millions of users is a high-value target. A successful attack on the custodian's key infrastructure can result in losses across the entire user base simultaneously, with recovery depending entirely on the custodian's reserves and insurance arrangements. **When Custodial Arrangements Make Sense** For small convenience balances, fiat on-ramps, or short-term trading activity, custodial platforms offer genuine practical benefits. Speed, simplicity, and fiat liquidity are real advantages in the right context. The risk becomes disproportionate when custodial accounts hold meaningful savings or long-term positions. For any DeFi yield strategy of size, self-custody is the appropriate starting point.
Non-Custodial Wallets: Full Control, Full Responsibility
**How Non-Custodial Wallets Work** A **non-custodial wallet** is one where you generate and hold the private key yourself. No third party has access. The wallet software generates a **seed phrase** during setup, which is the master backup from which the private key and all derived addresses can be regenerated. Whoever holds the seed phrase controls the wallet, unconditionally and permanently. This structure is the foundation of genuine self-sovereignty in DeFi. It also means every security responsibility rests with the user. There is no support line to call if you lose your seed phrase. There is no account recovery option that does not require the seed phrase itself. Your wallet is only as secure as your seed phrase storage. **Self-Custody Risks Most Guides Skip** **Seed phrase theft** is the most common self-custody failure mode. Phishing websites, browser-injected malware, fake wallet apps, and social engineering attacks are all designed to capture seed phrases from unsuspecting users. The attack surface is wide because seed phrase theft requires no cryptographic attack, only access to wherever the phrase is stored. Private key exposure from browser wallets running on compromised devices is a closely related risk. Hot wallets that store private keys in browser storage or application memory are vulnerable to any malware with read access to those locations. A compromised device can expose a key even if the user has never willingly shared their seed phrase with anyone. Inheritance and access-loss risk is underappreciated across the self-custody community. If a user dies or becomes incapacitated without leaving clear seed phrase instructions for a trusted person, the funds in that wallet become permanently inaccessible. There is no probate process for on-chain assets held in self-custody and no court order that can regenerate a lost key. Storing seed phrases digitally, including in screenshots, cloud notes, email drafts, or messaging apps, dramatically increases theft exposure. Any breach of those services can expose the phrase to an attacker who may not immediately use it, but will have permanent access to all assets the phrase controls. **The Self-Custody Paradox in DeFi** This is the insight most DeFi guides miss entirely. Having a non-custodial wallet does not make your DeFi deposits safe. Your wallet stays in your control throughout every interaction. But once you sign a deposit transaction and your funds enter a smart contract, the protocol becomes the effective custodian of those funds. Your wallet security and your deposit security are entirely separate problems. A perfectly secured hardware wallet holding a seed phrase engraved in metal cannot protect funds that are already sitting inside a vulnerable smart contract. The two risk surfaces do not overlap, and addressing one does nothing for the other.
Smart Contract Custody: The Layer Most Users Forget
**What Smart Contract Custody Means** **Smart contract custody** is the condition that exists when you deposit funds into a DeFi protocol. The protocol's code holds your assets and determines under what conditions you can retrieve them. You can only withdraw if the contract logic permits it, under the conditions it was written to allow. There is no human override, no emergency hotline, and no legal recourse if the contract behaves unexpectedly or is compromised. This is the most consequential custody layer for DeFi yield participants and the one that receives the least attention in mainstream crypto education. When someone asks whether their money is safe in DeFi, the wallet security answer is largely irrelevant if they have deposited into a poorly governed or exploitable protocol. 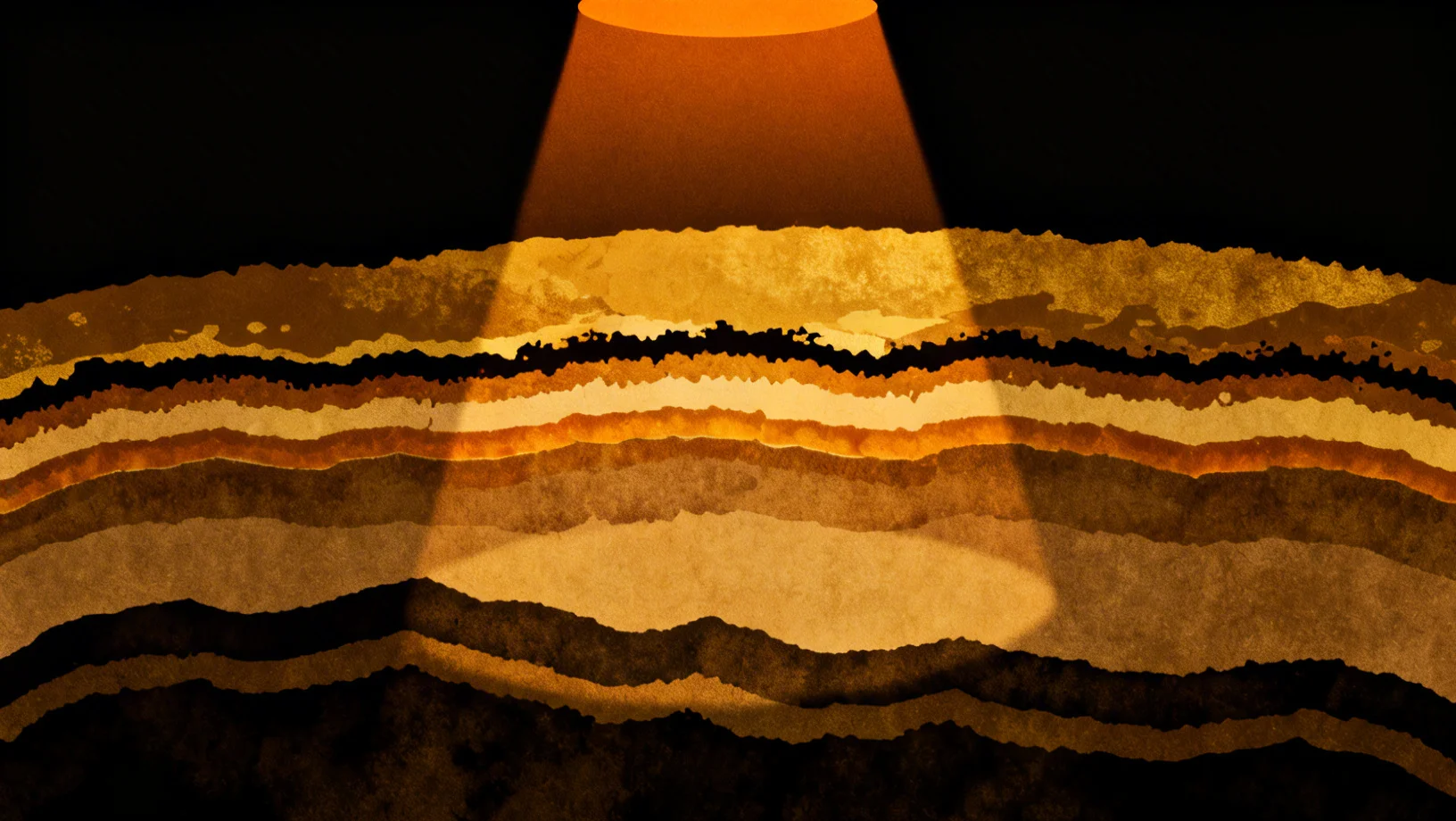 **Smart Contract Custody Risks** Code vulnerabilities are the most direct risk. DeFi exploits typically target one of a small set of known vulnerability patterns: reentrancy, oracle price manipulation, flash loan-enabled logic attacks, and arithmetic errors. Audits reduce but do not eliminate this exposure. Protocols that have operated for longer periods across multiple market conditions have had more opportunity for vulnerabilities to surface and be patched. **Upgradeable proxy** contracts introduce a layer of trust that is often overlooked by depositors. Many protocols, particularly on EVM chains, deploy behind a proxy pattern that allows the team to update the underlying contract logic after launch. From a depositor's perspective, an upgradeable contract means that what you deposit into today may not be governed by the same logic that controls withdrawals in the future. **Admin key** and owner key risk extends this problem further. Most DeFi protocols maintain a privileged address that can modify key parameters: interest rate models, collateral ratios, whitelisted tokens, and in some cases the contract logic itself. If this address is a single externally owned account with no timelock, a compromised deployer key can be used to drain the protocol before any monitoring tool or user can react. Governance attacks are a related mechanism. Protocols with token-based governance can be exploited through malicious proposals that, once passed, redirect treasury funds or alter critical protocol parameters. Flash loan-powered governance attacks have been executed against live protocols with real depositor funds at stake. **Protocol insolvency** is the custody risk most closely associated with lending protocols. When bad debt accumulates faster than protocol reserves can absorb it, a bank run dynamic emerges. Users who withdraw first are made whole; those who withdraw later bear the shortfall. This is a custody risk even if no hack occurs and no malicious actor is involved. **Upgrade Authority Risk on Solana** Solana introduces a specific mechanism called the **program upgrade authority**. When a Solana program is deployed, a designated account holds the authority to redeploy new bytecode to that program address. If this authority is active, the program logic can be changed at any time by whoever controls that account. You can verify the upgrade authority status of any Solana program on-chain using a block explorer or the Solana CLI. The [Solana documentation](https://docs.solana.com/cli/deploy-a-program) covers how to check program deployment status and upgrade authority settings directly. An **immutable contract**, one where the upgrade authority has been set to null or revoked, cannot be modified after deployment. This gives depositors a stronger and verifiable guarantee about the rules governing their funds. The standard for responsible upgrade authority governance on Solana is the **Squads multisig**. When a protocol's upgrade authority is controlled by a Squads multisig with multiple independent signers, no single person can redeploy program logic unilaterally. The [Squads Protocol documentation](https://docs.squads.so) provides details on how these governance structures are configured and how to verify them on-chain. Responsible Solana protocols either revoke the upgrade authority entirely or govern it through a transparent multisig arrangement.
Hardware Wallets vs Software Wallets for DeFi
**What Hardware Wallets Actually Protect Against** A hardware wallet stores the private key on a dedicated physical device designed to never expose that key to an internet-connected environment. All transaction signing occurs on-device. Malware running on your computer cannot extract the key because it never leaves the hardware module. This protection is real and meaningful for what it covers. If your laptop is compromised by a keylogger or a browser extension running malicious code, your hardware wallet private key remains secure on the device. The signing hardware is the gatekeeper, and software cannot bypass it. What hardware wallets do not protect against is equally important to understand. **Blind signing**, the act of approving a transaction without verifying its fully decoded details on the device screen, is a meaningful risk that users of hardware wallets introduce when they sign transactions quickly without reading them. If you sign a transaction that sends funds to a malicious contract because the details appeared legitimate on the browser interface, the resulting on-chain action is valid and irreversible regardless of how secure your key storage is.  **Software Wallets: The DeFi-Native Trade-Off** **Software wallets** such as browser extension wallets store the private key or a derived key in application memory or browser storage on an internet-connected device. This is inherently riskier than hardware storage from a key-exposure standpoint. Malware with sufficient access to browser storage can theoretically read those keys. For active DeFi interaction, however, software wallets offer substantial usability advantages. Transaction simulation, human-readable previews, protocol integration depth, and interaction speed all favor the software wallet experience. On Solana, Phantom and Backpack are the standard options, both of which offer transaction simulation features that flag suspicious activity before the user signs. The practical decision is not a binary choice between hardware and software. It is about allocating exposure appropriately across both. **The Layered Strategy: Hardware for Signing, Software for Browsing** The most effective model for active DeFi users combines hardware wallet key storage with software wallet connectivity. On Solana, this means using a Ledger device as the signing authority while connecting through Phantom or Backpack as the interface. Transaction approval happens on the Ledger screen, where the private key is protected from the browser environment entirely. A practical allocation approach: keep the bulk of long-term positions in a hardware-backed signing configuration and maintain only a small operational balance in a pure software wallet for frequent low-stakes transactions. This limits the worst-case loss from a software wallet compromise while preserving the usability of active DeFi participation. Always verify transaction details on the hardware device screen before confirming to avoid blind signing risk.
How to Evaluate Custody Risk Before Depositing
**A Pre-Deposit Custody Checklist** Understanding the theory of custody risk is only useful if it translates into specific actions before committing funds. The following checks address the most common custody failure modes and can be applied to protocols across any chain. **Is the protocol audited?** An audit is a review of a protocol's smart contract code by an independent security firm. It reduces but does not eliminate vulnerability risk. What matters is not simply whether an audit exists, but who conducted it, how recently it was performed, what scope it covered, and how the team responded to any issues found. An old audit on a partial codebase from an unfamiliar firm provides much weaker assurance than multiple recent audits by recognized specialists covering the full protocol. On Solana, reputable audit firms include OtterSec, Halborn, Zellic, and Neodyme. Look for audit reports that explicitly state the scope, list all findings with severity ratings, and confirm that critical and high-severity findings were resolved before deployment. **Is the contract upgradeable?** On EVM chains, check whether the protocol uses a transparent proxy or UUPS proxy pattern, both of which allow logic upgrades after deployment. On Solana, verify the upgrade authority status on-chain. An active upgrade authority means the program can be changed. A null upgrade authority means the program is immutable and what you deposit into today is governed by the same logic indefinitely. **Who controls the admin keys?** A protocol controlled by a single externally owned account is a concentrated risk. If that account is compromised, a single transaction can alter critical parameters or drain the protocol. The safer structure is a **multisig**, which requires multiple separate key holders to authorize any privileged action. Combine this with a **timelock**, a mandatory delay between a governance vote and its execution, and the window for identifying and responding to malicious proposals increases substantially. On Solana, Squads is the standard multisig solution for upgrade authority governance. **Does the protocol have a safety mechanism?** Some protocols operate safety modules or insurance pools that can absorb bad debt up to a defined threshold. These mechanisms provide an additional buffer but are not a complete safeguard. They typically cover specific scenarios, have hard coverage limits, and may require governance approval before funds are disbursed. Understand exactly what is covered and at what cap before treating insurance as a meaningful risk offset. **What is the protocol's track record?** Time since deployment is an imperfect but useful signal. A protocol that has operated without incident across multiple market cycles and periods of elevated volatility has had more opportunity for vulnerabilities to surface. TVL concentration is another factor worth examining: a protocol holding significantly more than its collateral base can safely back is carrying structural insolvency exposure that an audit cannot fix. The [Lince Tracker](https://yields.lince.finance/tracker/solana/category/lending) lets you compare Solana lending protocols side by side, including TVL, yield rates, and protocol-level metadata, which helps identify the most established and battle-tested options before depositing. For a broader set of metrics to verify before committing capital, the [DeFi Pool Deposit Checklist](/blog/risk-management/defi-pool-deposit-checklist-metrics) covers additional risk dimensions beyond custody that are worth reviewing in parallel.
Common Misconceptions About DeFi Custody
**"Non-custodial wallet means my DeFi funds are safe"** This is the most widespread misconception in DeFi self-custody discussions. Wallet security and deposit security are separate problems that do not overlap. A perfectly secured self-custodial wallet does nothing to protect funds that are already inside a vulnerable smart contract. Once you sign a deposit transaction, your wallet remains under your control and your funds are in the protocol's custody until you withdraw them. **"Audited means secure"** Audits are valuable and their absence is a serious warning sign. But an audit is not a guarantee of security. It tests for known vulnerability patterns within the scope of what was reviewed at the time it was conducted. Zero-day exploits, logic errors outside the audit scope, vulnerabilities in integrated third-party protocols, and issues introduced by post-audit upgrades are all outside the typical audit boundary. An audit is one important signal among several, not a binary clearance to proceed. **"I can always withdraw if the protocol is hacked"** Exploit transactions on DeFi protocols typically move faster than any user can react. A sophisticated attacker using flash loans can borrow, exploit, and repay within a single atomic block. By the time on-chain monitoring tools generate alerts and users begin initiating withdrawal transactions, the funds may already be gone. Protocol pauses, when they exist, are also handled by the protocol's own governance mechanisms, which can themselves be targeted. Assuming you can front-run an active exploit is not a viable risk management strategy. **"Hardware wallets protect me from DeFi hacks"** Hardware wallets protect your private key from being extracted by malware or remote attacks. They do not protect funds you have already deposited into a protocol. A hardware wallet cannot retract a valid signed transaction, cannot recall funds from an exploited contract, and cannot prevent a governance attack from redirecting treasury assets. The protection a hardware wallet provides is at the key layer. The protocol layer is a separate risk surface that hardware cannot touch.
Conclusion
DeFi custody risk operates across three layers and most guides only address one of them. Wallet security determines who can initiate transactions from your address. Protocol custody determines what happens to funds once they are deposited. Smart contract architecture, upgrade authorities, admin keys, and governance mechanisms all sit beneath the surface and create risks that wallet security cannot touch. The practical takeaway is straightforward: evaluate custody at both layers before every deposit. Check who controls the signing keys for privileged protocol actions, whether the contract logic is upgradeable, how long the protocol has operated without incident, and what the audit history looks like. Apply this evaluation before committing meaningful capital to any new protocol, regardless of its advertised yield rate. If you are looking for Solana yield strategies built around audited smart contracts and a non-custodial design, [Lince Smart Vaults](https://yields.lince.finance/vaults) offer a starting point for putting this framework into practice. The underlying approach to custody architecture is consistent with the evaluation criteria outlined in this guide.
FAQ
### What is custody risk in DeFi? Custody risk in DeFi refers to the possibility of losing access to your funds because of who or what controls them at a given layer. This includes the risk of a custodial exchange becoming insolvent, a smart contract being exploited, an admin key being compromised, or an upgradeable contract being modified in a way that harms depositors. Custody risk exists at the wallet layer, the protocol layer, and the smart contract infrastructure layer, and each requires separate evaluation. ### What is the difference between a custodial and non-custodial wallet? A custodial wallet is one where a third party holds your private key. You hold an IOU. A non-custodial wallet is one where you hold your private key directly and no third party can access your funds without it. The key distinction is that custodial arrangements create a dependency on the custodian's solvency, security, and willingness to honor withdrawals. Non-custodial arrangements eliminate that dependency but shift all security responsibility to the user. ### Can I lose funds in DeFi even if I use a hardware wallet? Yes. A hardware wallet protects your private key from being extracted by malware or remote attacks. It does not protect funds you have already deposited into a DeFi protocol. If the protocol is exploited, if its admin keys are compromised, or if a governance attack redirects treasury funds, the hardware wallet offers no protection against those outcomes. Wallet security and deposit security are distinct risk categories that require separate attention. ### What is smart contract custody risk? Smart contract custody risk is the risk that funds deposited into a DeFi protocol could be lost because of a flaw, vulnerability, or deliberate action in the smart contract code that governs them. Once you deposit, that contract holds custody of your funds. Exploits targeting code vulnerabilities, upgradeable proxy modifications, admin key abuse, and governance attacks are all mechanisms through which smart contract custody can fail even when the depositor's own wallet is fully secure. ### How do I check if a DeFi protocol is non-custodial? Verify that users retain their private keys throughout the deposit process and that the protocol cannot unilaterally block withdrawals. Then investigate the smart contract layer: is the contract upgradeable? Who controls the upgrade authority? Is a multisig with a timelock in place for privileged protocol actions? A genuinely non-custodial model means no single party can modify the contract logic or redirect funds without a transparent governance process and a mandatory delay that gives depositors time to exit. ### What is upgrade authority risk in Solana DeFi? On Solana, every deployed program can optionally have a designated account called the upgrade authority, which holds the ability to redeploy new bytecode to that program address. If the upgrade authority is active, program logic can be changed at any time by whoever controls that account. The risk is that a compromised or malicious upgrade authority could modify protocol behavior after your funds are deposited. Responsible protocols either revoke the upgrade authority to make the program immutable or govern it through a Squads multisig with multiple independent signers, making unilateral changes impossible. ### Is self-custody the safest option in DeFi? Self-custody eliminates custodian insolvency risk and third-party access risk at the wallet layer. However, it introduces personal responsibility risk including seed phrase loss, theft, and inheritance failure. More importantly, self-custody of your wallet does not address protocol-level custody risk. Depositing funds into a poorly governed smart contract from a self-custodial wallet still fully exposes those funds to smart contract risk. The safest overall approach combines strong self-custody practices at the wallet layer with rigorous protocol custody evaluation before each deposit. ### What happens to my funds if a DeFi protocol becomes insolvent? Protocol insolvency in DeFi typically unfolds as a bank run dynamic. If a lending protocol accumulates bad debt that exceeds its reserves, users who withdraw first are made whole while later withdrawers may receive less or nothing. Unlike traditional bank insolvency, there is no deposit insurance, no regulatory receiver, and no legal recovery mechanism. Understanding the collateralization model and bad debt absorption capacity of any protocol you deposit into is therefore a direct element of custody risk evaluation, not a secondary concern.